

Implementando conceptos innovadores en silicio


Un año más, el Instituto de Microelectrónica de Sevilla ha estado presente en la Feria de la Ciencia, que ya alcanza su 24ª edición.
14 Mayo 2026

A través de un laberinto láser y retos criptográficos, investigadores del centro acercaron conceptos clave de protección digital a cientos de estudiantes procedentes de toda Europa.
26 Marzo 2026
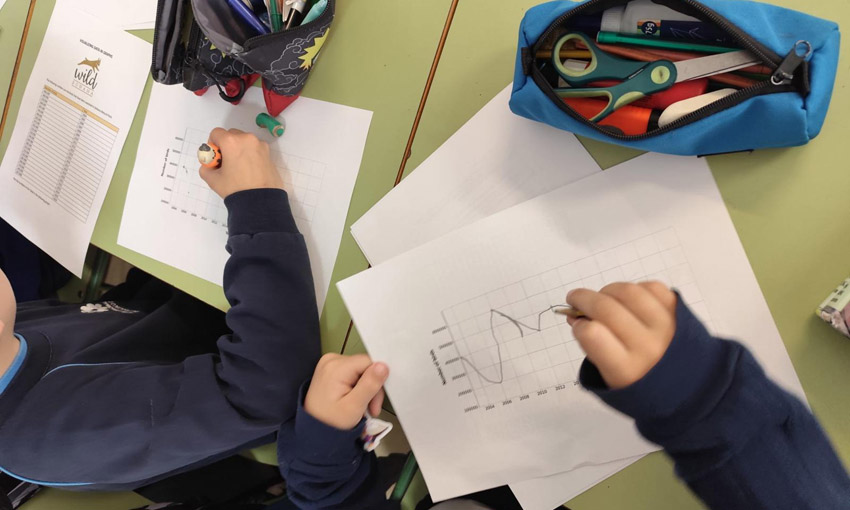
Investigadores del IMSE llevan la divulgación científica a centros educativos con motivo del Día Internacional de las Matemáticas.
16 Marzo 2026

Desde el IMSE llevamos a cabo varias actividades para poner en valor en papel de las investigadoras de nuestro centro.
2 Marzo 2026

"Science is Wonderful!", la Feria Internacional de la Ciencia organizada por la Comisión Europea, se celebrará en Bruselas los próximos 18, 19 y 20 de marzo de 2026, y volverá a contar por tercer año consecutivo con la participación de un equipo de investigadores del Instituto de Microelectrónica de Sevilla (IMSE-CNM).
3 Noviembre 2025

El talento investigador del IMSE vuelve a destacar con el Premio "Leonardo Torres Quevedo" concedido a Pablo Navarro por su Trabajo de Fin de Máster que profundiza en la seguridad y eficiencia de algoritmos criptográficos.
31 Octubre 2025
An FPGA-Based Event-Timing Front-End for Time-Resolved Sensing with Dual-Mode Experimental Characterization
J. Núñez and R. Fiorelli
Journal Paper · Sensors 2026, 26, 3268
MDPI ISSN: 1424-8220
resumen
doi
Simulated VO2 Neuron With Embedded HfO2 Memristive Synapse
J. Núñez and R. Fiorelli
Journal Paper · IEEE Electron Device Letters, vol. 47, no. 5, pp. 1025-1028, May 2026
IEEE ISSN: 1558-0563
resumen
doi
Robust and Scalable Cell-Based 65-nm CMOS RO-PUF Implementation
P. Ortega-Castro, E. Camacho-Ruiz, J.M. Mora-Gutiérrez, P. Brox and M.C. Martínez-Rodríguez
Journal Paper · IEEE Open Journal of the Solid-State Circuits Society (Early Access)
IEEE ISSN: 2644-1349
resumen
doi
Assessment of an FPGA Implementation of a Hybrid PUF Based on a Configurable Transient Effect Ring Oscillator and Ring Oscillator (TERORO-PUF)
A. Casado-Galán, J. Núñez, E. Tena-Sánchez, F.E. Potestad-Ordóñez and A.J. Acosta-Jiménez
Journal Paper · Electronics, vol. 15, no. 3, article 661, 2026
MDPI ISSN: 2079-9292
resumen
doi
El área de especialización del Instituto es el diseño de circuitos integrados analógicos y de señal mixta en tecnología CMOS, así como su uso en diferentes contextos de aplicación tales como dispositivos biomédicos, comunicaciones inalámbricas, conversión de datos, sensores de visión inteligentes, ciberseguridad, computación neuromórfica y tecnología espacial.
La plantilla del IMSE-CNM está formada por unas cien personas, entre personal científico y de apoyo, que participan en el avance del conocimiento, la generación de diseños de alto nivel científico-técnico y la transferencia de tecnología.